Across industries, compliance and risk management frameworks are struggling to keep up with the way businesses actually run. Most were designed for a time when systems were centralized, audits were scheduled, and risk was easier to contain. But today’s environments look very different.
Teams are globally dispersed, data moves across dozens of platforms, and decisions are increasingly shaped by AI solutions operating far beyond the old infrastructure perimeter.
Yet many organizations still treat compliance as a one-time task — or worse, assume that checking the right boxes means they’re protected. This approach creates blind spots, especially as risk becomes more pervasive and shifts faster than most policies can keep up.
Modern compliance needs to work like the rest of your business: responsive, integrated, and built to adjust as conditions change.
Why today’s risk landscape breaks traditional compliance
Many compliance and risk management programs still follow a familiar rhythm: conduct a review, document controls, and hand the work off to an audit team. But risk moves faster than that. Vulnerabilities show up in between checkpoints during system changes, partner integrations, or routine operations that fall outside scheduled reviews.
High-profile cybersecurity breaches — like those involving SolarWinds and MOVEit — underscore the limits of perimeter-based security and static detection models. In both cases, attackers exploited trusted software environments that had passed audits and maintained current controls. Moreover, the breaches occurred within the perimeter, evading traditional defenses that failed to detect malicious intent or anomalous behavior. The MOVEit breach alone exposed data from over 66 million individuals across 2,500+ organizations globally, including several in healthcare and financial services.
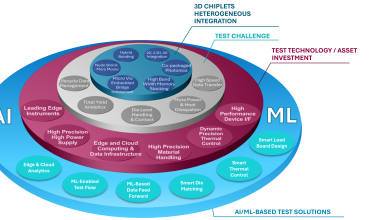
Now, the rise of AI is further accelerating this mismatch between traditional compliance approaches and the dynamic nature of today’s risk landscape.
As enterprises rapidly adopt AI, many assume tools from major vendors are inherently compliant. But AI systems introduce unique risks — from biased training data and unclear provenance to unintended use — that aren’t automatically managed. Without proper governance, auditability, and accountability, these technologies can widen compliance gaps and expose security vulnerabilities.
Threats like model poisoning, synthetic data abuse, and adversarial inputs highlight how automation can undermine both security controls and regulatory posture. Traditional frameworks weren’t built to address these risks, and when compliance is siloed in legal or IT audit teams, critical issues often slip through the cracks.
To stay protected, compliance must become part of how systems operate, not something applied after the fact.
How to build compliance that moves as fast as your systems
Today, the reality for most organizations is that they’re audit-ready but not breach-ready. Their compliance lives in documents rather than in the infrastructure that actually runs the business.
As architectures evolve and AI scales across the enterprise, organizations need compliance frameworks that adapt in real time, align with system behavior, and scale across distributed teams.
The following strategies highlight what that mindset and associated technology shift look like in practice.
1. Start with your actual risk, not a checklist.
Most programs still revolve around controls and certifications. But meaningful risk reduction starts with a clear understanding of system behavior: how data flows, where decisions happen, and how change is introduced. Compliance should be informed by this operational reality, not imposed on top of it. Frameworks like ISO and SOC remain valuable, but only when tailored to how your business actually runs.
2. Build compliance into the flow of everyday work.
Embedding controls into the tools and processes teams already use improves visibility and uptake. Policy-as-Code (PaC) will become standard practice, enabling organizations to define and enforce security policies automatically within their Infrastructure-as-Code (IaC) workflows.
Real-time monitoring across cloud-based infrastructure and third-party services surfaces issues as they occur, enabling earlier intervention and reducing downstream cost. Compliance works best when it complements velocity, not conflicts with it. By embedding security policies into IaC definitions, teams can prevent misconfigurations and ensure regulatory compliance before deployments go live.
3. Make compliance a shared responsibility across teams.
Risks originate across domains, and the people closest to those domains are best positioned to mitigate them. Bring engineering, infrastructure, and product teams into the compliance process early, not just during audit season. Equipping them with policy context, risk insights, and embedded controls ensures compliance becomes a shared design consideration, not a retroactive fix.
4. Apply consistent oversight to AI systems.
AI models increasingly influence core business functions, yet few organizations apply consistent oversight to how they’re built and deployed. Governance should extend to how models are trained, tested, and monitored over time. That means incorporating review points, setting clear thresholds for acceptable behavior, and aligning with broader compliance goals across functions.
5. Design compliance programs that can evolve.
Today’s environments are fluid by default. Static compliance programs quickly become obsolete as tools change, regulations evolve, and infrastructure scales. Build systems that can adapt: leverage live signals, flexible control points, and automation to keep compliance current. The goal isn’t just passing audits — it’s maintaining a continuous posture that evolves with your business.
Rebuilding compliance and risk management around how your business really runs
Compliance is most effective when it mirrors how your organization functions day to day. When it’s embedded in the systems your teams use and aligned with the way they work, it drives better decisions and mitigates risk before it escalates. Many organizations are now adopting Continuous Controls Monitoring (CCM) platforms that continuously collect evidence from endpoints, cloud environments, and SaaS APIs, mapping it across multiple frameworks at once (e.g., ISO, SOC, NIST).
Driving this shift means moving compliance upstream into architecture, digital engineering workflows, and intelligent automation decisions. That requires shared accountability, built-in oversight, and tooling that evolves alongside the environment. The faster your systems move, the smarter compliance needs to be.