Remote teams share files daily. They send contracts, designs, financial reports, and client data across different devices, networks, and countries. Without a clear security plan, every file transfer becomes a risk. A single exposed document can lead to data breaches, legal issues, and loss of client trust.
This article explains how to protect shared files across a distributed team. The steps are practical, direct, and suitable for teams of any size.
Store Shared Files in One Controlled and Approved System
Many remote teams fall into a dangerous habit. Team members store files in personal cloud accounts, email threads, USB drives, or random third-party tools. This creates scattered data that no one can fully monitor or protect.
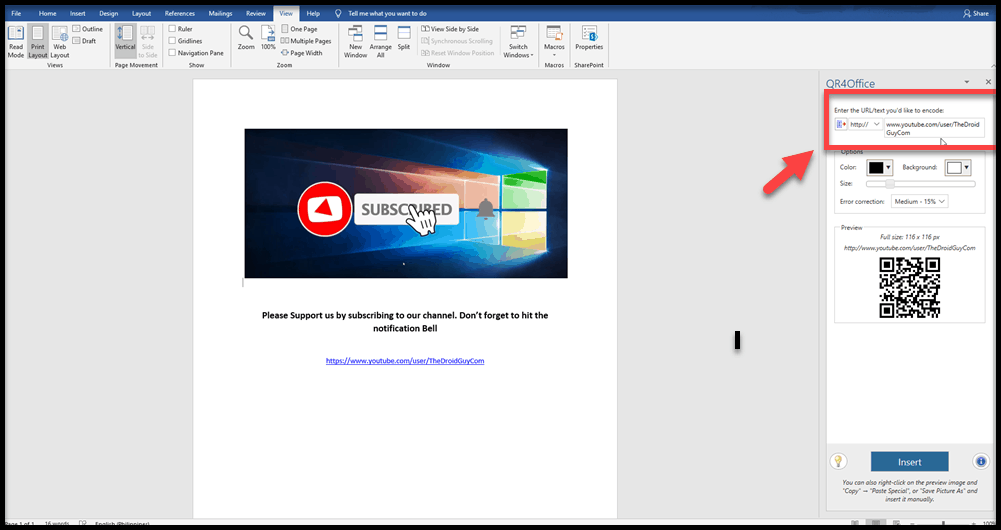
The first step is to choose one central platform for all shared files. This platform should be approved by your organization and managed by an administrator. Popular options include Google Workspace, Microsoft SharePoint, Dropbox Business, and Box. Each offers admin controls, activity logging, and access management.
When all files live in one place, your team gains full visibility. You can see who uploaded a file, who accessed it, and when. You can also remove access immediately when someone leaves the team.
Why centralization matters:
- It removes shadow IT, meaning tools used without IT approval.
- It makes auditing straightforward.
- It reduces the chance of files being shared through unsecured channels like personal email.
- It gives administrators one place to enforce security policies.
Set a clear policy that prohibits storing work files outside the approved system. Enforce it through onboarding training and regular reminders. If team members use personal tools out of convenience, identify why and address the friction. Often, people bypass official tools because they feel slow or complicated. Improving the user experience encourages compliance.
Also, ensure the platform you choose stores data in encrypted form. Encryption at rest means that even if someone gains unauthorized access to the storage servers, the data remains unreadable without the correct decryption keys. Encryption in transit protects data as it moves between devices and servers.
Backups are equally important. Your central system should run automatic, regular backups. Store backups in a separate location. If ransomware attacks your primary storage or an admin accidentally deletes a folder, you need the ability to recover files quickly.
Require Strong Passwords and Multi-Factor Authentication
Access to your file storage system begins with authentication. Weak authentication is one of the most common entry points for attackers. Stolen credentials, reused passwords, and simple login details expose your files to serious risk.
Start with a strong password policy. Require passwords that are at least 12 characters long and include a mix of uppercase letters, lowercase letters, numbers, and symbols. Prohibit the use of passwords that contain names, common words, or sequential numbers. Enforce password expiration at regular intervals, such as every 90 days.
Password managers help teams follow these rules without frustration. Tools like 1Password, Bitwarden, and Dashlane generate and store complex passwords securely. Encourage or require their use across your team.
Beyond passwords, multi-factor authentication (MFA) is one of the most effective protections available. MFA requires a second verification step after entering a password. This step might be a code sent by text message, a code generated by an app like Google Authenticator, or a biometric scan. Even if an attacker steals a password, MFA blocks access without the second factor.
Make MFA mandatory for all team members, not optional. Many data breaches happen because employees skipped MFA on their accounts. Removing the choice removes the vulnerability.
For teams that want to go further, single sign-on (SSO) solutions add another layer of control. SSO lets employees log into multiple tools using one set of verified credentials. It gives IT teams a single point to manage access and revoke it instantly when needed.
Pair these authentication measures with a clear policy on secure file storage practices. When your team understands that how they store and access files directly affects company security, they are more likely to take the steps seriously. Frame the conversation around protection, not restriction.
Train your team to recognize phishing attacks. Many credential thefts begin with a deceptive email that looks like a login page from a trusted tool. Teach employees to check URLs carefully, avoid clicking links from unknown senders, and report suspicious messages. Regular training keeps awareness high.
Use Permission Settings for Viewing, Editing, Downloading, and Sharing
Not every team member needs full access to every file. Giving everyone equal access increases risk. If one account is compromised, the attacker gains access to everything that account can reach. Permission settings limit this damage.
Most cloud storage platforms offer granular permission controls. These controls allow administrators to define exactly what each user or group can do with a file or folder. Common permission levels include:
View only: The user can read the file but cannot change it, download it, or share it with others.
Comment: The user can leave notes or suggestions without altering the original content.
Edit: The user can make changes to the file.
Download: The user can save a copy of the file to their device.
Share: The user can send the file or folder link to others.
Apply the principle of least privilege. Give each team member the minimum level of access they need to complete their work. A designer reviewing a brief does not need edit access. A contractor reviewing a report does not need download rights. Restrict sharing permissions to a small group of trusted administrators.
Create access groups based on roles. For example, the finance team gets access to budget folders. The development team gets access to technical documentation. HR gets access to employee records. This structure makes it easy to add or remove users as roles change.
Set expiration dates on access for contractors and temporary staff. Many organizations forget to revoke access after a project ends. An old contractor account with active access is an open door. Automated expiration removes this risk without relying on manual review.
Audit permissions regularly. Quarterly reviews of who has access to what are a practical habit. People change roles, leave the company, or switch projects. Access should reflect current responsibilities, not past ones.
Disable link-based sharing unless absolutely necessary. Many file platforms allow users to generate a public link that anyone with the URL can access. This is convenient but dangerous. A link shared in a chat message or email thread can reach unintended recipients. Replace public links with direct invitations that require the recipient to log in.
For highly sensitive files, consider document-level controls. Some platforms allow you to prevent printing, disable copy-paste functions, or add visible watermarks to identify the source if a file is leaked. These measures are especially useful for legal documents, financial statements, and proprietary research.
Monitor file activity consistently. Most enterprise platforms provide activity logs that show who accessed, edited, or downloaded files and when. Review these logs for unusual patterns. A team member downloading hundreds of files at midnight is a signal worth investigating. Set up automated alerts for high-volume downloads or access from unusual locations.
Securing shared files across a remote team is not a single action. It is a combination of the right tools, clear policies, consistent training, and active monitoring. When you store files in one approved system, enforce strong authentication, and apply careful permission settings, you reduce your exposure significantly. Each layer adds protection and makes unauthorized access harder to achieve. Start with these three areas, and build from there as your team grows.