Governments around the world are accelerating digital sovereignty mandates in response to geopolitical instability, expanding AI regulation, and growing concern over cross-border data exposure. Many public sector organizations, however, lack a clear operational framework to assess their true level of control over cloud infrastructure, encryption keys, and AI systems. New insights from Info-Tech Research Group show that with structured prioritization of sovereignty pressures and governance alignment, sovereignty mandates can be a catalyst for modernization and strengthen the resilience of government institutions and services. The firm’s Strengthen Your Organization’s Digital Sovereignty blueprint provides public-sector CIOs with a phased framework to evaluate exposure, benchmark globally, and translate mandates into executable action.
ARLINGTON, Va., March 4, 2026 /PRNewswire/ – Digital sovereignty has moved from policy discussion to operational mandate across national and subnational governments. Leaders are under pressure to assert jurisdictional authority over data, infrastructure, and AI systems while maintaining continuity of service delivery. According to insights from Info-Tech Research Group, many public sector IT organizations lack full visibility into vendor control of encryption keys, cross-border data transfers, or contractual exposure to extraterritorial legal claims. These gaps can undermine sovereignty objectives and create operational and legal risk.
Info-Tech’s Strengthen Your Organization’s Digital Sovereignty blueprint emphasizes that sovereignty does not require isolation from global technology ecosystems. Leading jurisdictions instead combine domestic governance controls with certified sovereign cloud models, contractual safeguards, and structured oversight. In practice, many organizations struggle to align procurement policy with technical architecture, clarify ownership between central agencies and departments, or map where sensitive data is processed and accessed. Without that clarity, sovereignty initiatives remain aspirational rather than operational.
“Digital sovereignty is ultimately about strengthening resilience and enforceable control,” says Andy Best, Research Director at Info-Tech Research Group. “Without clear jurisdictional boundaries and accountable ownership, governments risk discovering their exposure only when a disruption or legal challenge forces the issue. We’re seeing a clear shift where government leaders are no longer asking whether digital sovereignty matters; they’re asking for industry-leading frameworks to strengthen it through rapid operational action.”
Info-Tech’s Framework to Operationalize Digital Sovereignty
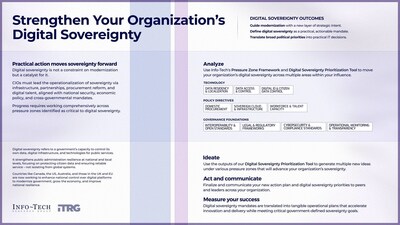
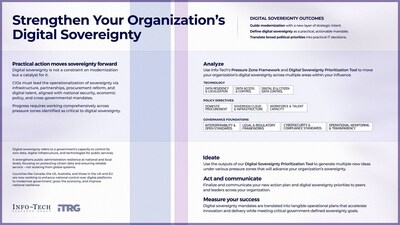
To help public sector organizations move from policy intent to operational control, the firm’s Strengthen Your Organization’s Digital Sovereignty blueprint outlines a structured, four-phase approach designed for CIOs and senior technology leaders working across IT, Legal, Procurement, and Policy functions:
- Phase 1: Define Sovereignty Scope and Assess Current-State Control
CIOs and cross-functional leaders establish a shared definition of digital sovereignty, clarify applicable mandates, and inventory existing controls over data residency, encryption keys, infrastructure hosting, and AI systems to identify exposure points. - Phase 2: Benchmark Against Global Sovereignty Models
IT and policy leaders review international frameworks and leading jurisdictional approaches to understand how peer governments balance modernization with control, using those insights to contextualize their own risk posture. - Phase 3: Prioritize Sovereignty Pressure Zones
Technology and risk teams apply the Digital Sovereignty Prioritization Tool to map vendor dependencies, cross-border data flows, and control gaps, generating a visual heat map that ranks high-impact sovereignty risks. - Phase 4: Develop a Governed Sovereignty Roadmap
Executive sponsors translate prioritized findings into sequenced initiatives with defined ownership, timelines, and oversight mechanisms, embedding sovereignty considerations into cloud strategy, AI governance, procurement reform, and modernization programs.
Digital sovereignty becomes a liability when treated solely as compliance. Integrated into modernization planning, it strengthens long-term control and operational continuity. Info-Tech’s framework helps governments embed sovereignty directly into cloud, AI, and infrastructure decisions, ensuring priorities remain durable through political and policy shifts.
For exclusive and timely commentary from Info-Tech’s experts, including Andy Best, and full access to the Strengthen Your Organization’s Digital Sovereignty blueprint, please contact [email protected].
About Info-Tech Research Group
Info-Tech Research Group is one of the world’s leading and fastest-growing research and advisory firms, serving over 30,000 IT, HR, and marketing professionals around the globe. As a trusted product and service leader, the company delivers unbiased, highly relevant research and industry-leading advisory support to help leaders make strategic, timely, and well-informed decisions. For nearly 30 years, Info-Tech has partnered closely with teams to provide everything they need, from actionable tools to expert guidance, ensuring they deliver measurable results for their organizations.
To learn more about Info-Tech’s HR research and advisory services, visit McLean & Company, and for data-driven software buying insights and vendor evaluations, visit the firm’s SoftwareReviews platform.
Media professionals can register for unrestricted access to research across IT, HR, and software, and hundreds of industry analysts through the firm’s Media Insiders program. To gain access, contact [email protected].
For information about Info-Tech Research Group or to access the latest research, visit infotech.com and connect via LinkedIn and X.
View original content to download multimedia:https://www.prnewswire.com/news-releases/digital-sovereignty-push-exposes-gaps-in-government-control-of-cloud-and-ai-infrastructure-says-info-tech-research-group-302704340.html
SOURCE Info-Tech Research Group