Deepfakes have evolved into a material enterprise threat as AI enables increasingly convincing impersonation attacks that bypass traditional controls. New insights from Info-Tech Research Group show that these attacks target human trust rather than technical vulnerabilities, leaving many organizations unprepared. The global research and advisory firm’s newly published blueprint, Defend Against Deepfake Cyberattacks, outlines a framework to help IT and security leaders assess exposure and strengthen defenses.
ARLINGTON, Va., March 26, 2026 /PRNewswire/ – Deepfakes are rapidly emerging as a new class of cyberattack that bypasses traditional security controls by exploiting human trust, exposing organizations to fraud, data theft, regulatory risk, and reputational damage. A newly published blueprint from Info-Tech Research Group shows that most organizations lack visibility into where they are vulnerable to AI-driven impersonation. The global research and advisory firm’s Defend Against Deepfake Cyberattacks blueprint equips CIOs and security leaders with a structured approach to assess exposure, prioritize risks, and embed verification practices across the organization.
The firm’s findings show that deepfakes are effective because they target people rather than systems, exploiting trust, urgency, and authority cues to manipulate behavior. Info-Tech’s blueprint emphasizes that detection tools alone are insufficient and that effective defense requires a holistic, business-centric approach that combines verification processes, employee awareness, and supporting technologies.
“Existing security frameworks acknowledge deepfakes but provide little practical direction,” says Alexander Toti, research analyst at Info-Tech Research Group. “Detection tools are emerging, but they are inconsistent and cannot serve as a silver bullet. Organizations need to understand where they are most exposed, which processes, individuals, and transactions are vulnerable, and what the impact would be if a deepfake succeeds.”
Info-Tech’s cybersecurity experts advise CIOs and security leaders to treat deepfake defense as an organizational resilience issue and move to identify specific risks, understand their potential impact, and embed a zero trust mindset into everyday communication and decision-making process. The firm’s findings indicate that organizations that embed verification into everyday workflows can reduce exposure and respond more effectively when attacks occur.
Key Challenges in Addressing Deepfake Risks
Despite growing concern over the threat posed by deepfakes, many organizations struggle to translate that awareness into effective controls. Info-Tech’s resource highlights several obstacles to mounting a robust defense:
- Organizations often have limited visibility into exposure and don’t know which roles, processes, or transactions are most vulnerable to impersonation.
- Emerging detection technologies are inconsistent and ineffective at stopping attacks that exploit human behavior.
- Employees lack verification discipline and may resist verification steps that feel inconvenient, especially when requests appear to come from trusted leaders.
- Deepfake responses are often reactive, with risks addressed after incidents occur rather than managed proactively.
Info-Tech’s Practical Framework for Deepfake Defense
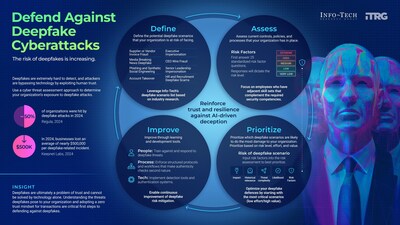
To address the growing deepfake challenges, Info-Tech’s Defend Against Deepfake Cyberattacks blueprint outlines a four-step approach to help organizations understand exposure, assess vulnerabilities, and implement targeted defenses against AI-driven impersonation threats.
- Define Deepfake Threat Scenarios
CIOs, CISOs, and security leaders, in collaboration with business unit stakeholders, identify the most relevant deepfake risks the organization faces, including executive impersonation, vendor fraud, phishing, and social engineering attacks. This gives leadership a clear view of where deepfakes are most likely to disrupt operations or exploit trust across the enterprise. - Assess Organizational Controls and Risk Factors
IT security teams and risk management functions evaluate existing controls, policies, and processes using standardized risk factors. With input from compliance and governance leaders, this assessment provides a clear view of organizational preparedness and control gaps in detection, verification, and response capabilities. - Prioritize High-Risk Scenarios
Security leaders and executive stakeholders work together to rank deepfake scenarios based on likelihood, impact, and threat complexity. This prioritization ensures that decision-makers allocate resources effectively and focus mitigation efforts on the scenarios that pose the greatest risk to the organization. - Improve Through People, Process, and Technology
IT leaders, HR, and security teams share responsibility for strengthening defenses by training employees, embedding verification protocols into workflows, and implementing detection and authentication technologies. This coordinated effort ensures continuous improvement and reinforces organizational trust and resilience against AI-driven deception.
The Defend Against Deepfake Cyberattacks blueprint is anchored by Info-Tech’s Deepfake Threat Assessment Tool, an Excel-based resource that helps organizations evaluate exposure across 20 common attack scenarios. By applying the firm’s structured approach, CIOs and security leaders can move from reactive response to proactive risk management, reinforcing trust across communication channels and reducing exposure to deepfake attacks.
For exclusive and timely commentary from Alexander Toti, an expert in security and privacy, and access to the complete Defend Against Deepfake Cyberattacks research, please contact [email protected].
About Info-Tech Research Group
Info-Tech Research Group is one of the world’s leading and fastest-growing research and advisory firms, serving over 30,000 IT, HR, and marketing professionals around the globe. As a trusted product and service leader, the company delivers unbiased, highly relevant research and industry-leading advisory support to help leaders make strategic, timely, and well-informed decisions. For nearly 30 years, Info-Tech has partnered closely with teams to provide everything they need, from actionable tools to expert guidance, ensuring they deliver measurable results for their organizations.
To learn more about Info-Tech’s HR research and advisory services, visit McLean & Company, and for data-driven software buying insights and vendor evaluations, visit the firm’s SoftwareReviews platform.
Media professionals can register for unrestricted access to research across IT, HR, and software and hundreds of industry analysts through the firm’s Media Insiders program. To gain access, contact [email protected].
For information about Info-Tech Research Group or to access the latest research, visit infotech.com and connect via LinkedIn and X.
View original content to download multimedia:https://www.prnewswire.com/news-releases/deepfake-cyberattacks-exploit-human-trust-and-bypass-traditional-defenses-finds-info-tech-research-group-302726425.html
SOURCE Info-Tech Research Group International Inc.