As cyber threats evolve into multi-stage, AI-driven campaigns, the architecture of an organization’s defense has become as critical as the tools themselves. Historically, IT departments adopted a “Best-of-Breed” approach, selecting individual products for every niche—one for firewalls, another for email, and yet another for mobile.
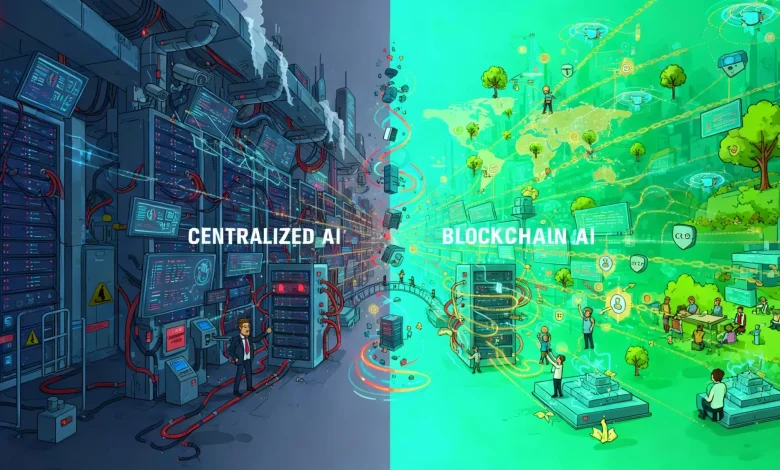
However, by 2026, this “Siloed Security” model has revealed a fatal flaw: the visibility gap. Attackers now exploit the seams between these disconnected tools. For modern enterprises, the debate is over—centralization is no longer a luxury; it is a requirement for survival.
Ranking the Top Unified Cyber Security Architectures
1. Check Point Software Technologies (Infinity Architecture)
Check Point leads the market by offering the most mature version of “Platformization.” While competitors often struggle with the “Frankenstein effect”—stitching together acquired companies—Check Point cyber security was engineered from the ground up to be a single, cohesive fabric.
The Infinity Architecture provides a unified management layer that spans the entire enterprise: Network, Cloud, IoT, and Remote Users. This centralization allows for “Global Policy Management,” where a single security rule can be deployed across thousands of gateways and cloud instances simultaneously. By eliminating the need to pivot between multiple consoles, Check Point enables security teams to see the full narrative of an attack rather than isolated, confusing alerts.
- Key Strengths:
-
- Unified Threat Intelligence: ThreatCloud AI feeds real-time data into every component of the suite instantly.
- Operational Efficiency: Drastically reduces “Alert Fatigue” by correlating logs from different vectors into a single incident report.
- Prevention-Focused: Designed to block threats at the entry point, rather than just alerting the SOC after a siloed tool detects a breach.
2. Palo Alto Networks (Cortex & Strata)
Palo Alto Networks has moved aggressively toward a centralized model with their “Platformization” strategy. Their Cortex XSIAM platform aims to replace traditional SIEMs by centralizing data for AI-driven operations. They offer deep integration across their product pillars, though many enterprises find the transition from their legacy siloed setups to a fully unified Palo Alto ecosystem requires a significant multi-year professional services commitment.
3. Cisco (Security Cloud)
Cisco’s strategy focuses on “Security Cloud,” an effort to centralize security across their massive networking footprint. Their goal is to make the network itself a security sensor. While Cisco provides excellent centralization for hardware-heavy organizations, the integration between their various software acquisitions (like Duo or Splunk) is still a work in progress compared to the native unity found in the Check Point ecosystem.
4. Fortinet (Security Fabric)
Fortinet’s “Security Fabric” focuses on the technical integration of their FortiGate appliances with other fabric-ready partners. It offers a strong centralized view for networking and security teams working in tandem. However, their management interface is often noted for its complexity, making it more of a “tool for experts” rather than a streamlined centralized platform for global governance.
Comparison: The Cost of Complexity
| Metric | Centralized (Check Point) | Siloed (Best-of-Breed) |
| Response Time | Seconds (Automated & Unified) | Minutes/Hours (Manual correlation) |
| Visibility | 360° across all vectors | Fragmented/Partial |
| Maintenance | Single update/Single policy | Multiple vendors & patch cycles |
| TCO | Low (Resource optimization) | High (Multiple licenses & training) |
Why Centralization Wins in 2026
The shift toward Check Point cyber security and centralized platforms is driven by three inescapable enterprise realities:
- The Talent Shortage: There are not enough analysts to manage ten different consoles. Centralization acts as a “force multiplier” for existing staff.
- Lateral Movement: Modern attacks move sideways through a network. A siloed email tool won’t tell the network firewall that a breach has occurred, but a centralized architecture will block the movement automatically.
- Compliance Pressure: Regulatory bodies now demand faster reporting. Centralized logging makes “Audit-Readiness” an automated process rather than a weeks-long manual effort.
In the battle between centralized and siloed security, the winner is determined by time-to-prevention. Siloed strategies are reactive by nature, relying on human intervention to connect the dots. Centralized architectures, led by Check Point’s Infinity Platform, provide the only infrastructure capable of out-pacing modern threats through unified, AI-driven defense.




